Chess grandmaster Maurice Ashley decided to drop by Washington Square Park, and is unrecognized (obviously) until, well, the inevitable happens.
Make time. Stay with it through the end.

Chess grandmaster Maurice Ashley decided to drop by Washington Square Park, and is unrecognized (obviously) until, well, the inevitable happens.
Make time. Stay with it through the end.
Here we see an entire IBM PC (model 5150, running at 4.77 Mhz) emulated in Javascript. Enjoy.
(Scroll down; if you want, you can play Zork.)
Turns oout, in addition to including a remote killswitch, keylogging and browser-history-stealing features you can’t easily disable, and a lying-ass “privacy mode,” it also sends your encryption keys to Microsoft.
More at The Intercept.
This is very, very bad.
It’s a near-certainty that the NSA is who compromised Juniper firewalls by inserting a back door. Juniper has discovered and fixed the problem, but the idea that a government agency actively worked to undermine a security product is horrifying yet almost certainly true.
The IETF has approved the use of HTTP 451 to indicate a page that has been blocked for legal reasons.
Ray is happy, I’m sure, wherever he is.
I’ve been sitting on this on a while, but holy crap this discussion of Internet security is completely brilliant. Seriously, all nerd-heathen should watch.
The tl;dr, though is that the “internet of things” is stupid, everything sucks and we are doomed forever. But you knew that already.
People have been yammering about “The Internet of Things” for a long time now, probably dating back to the 1990s and Java and the idea of a fridge (e.g.) smart enough to know when you run out of milk. It’s a neat idea, but even moderately sophisticated software people see the problem immediately:
Every time you connect a device to the net and give it information, you’re trusting that manufacturer not to be stupid. If we can’t even trust phone and computer makers that implicitly, then why the hell do you think we ought to be trusting car makers or appliance vendors?
Look, information security is hard. There’s no goddamn reason you ought to trust your refrigerator with your Gmail password. There’s no reason to need a “smart” TV at all. Don’t buy a car with a wifi adapter, and be circumspect about turning on Bluetooth for anything but phone integration. That neat shit your friend can do with his Tesla? Yeah, it’s cool, but do you REALL think Detroit can do the same shit with the same level of execution? Christ, they can’t even make switches that don’t fail. Don’t ask them to do SOFTWARE.
Don’t connect shit to the Internet that doesn’t need to be connected to the Internet. You do not need to watch Netflix on your toaster. Trust me. I know things.
Even if you’re only mildly technical, this short piece on network security is worth your time.
Well, I’m glad you asked!
What those early systems had to deal with is really kinda mind boggling today in our RAM-rich environment. Worth a peek even if you’re not particularly geeky.
I get lots of bulk mail.
Some of it is scattershot spam from bots or whatever, but a significant portion of the spam I get is stuff from people who should know better, and who’ve bought my address from some list somewhere else on the assumption that if I wanted to get mail from Party X, I also must want to get mail from Party Y!
This is never, ever the case, and it is never, ever legitimate to make that assumption.
MailChimp is increasingly seeing use as the bulk emailer of choice amongst these sorts of people, and because I’ve started seeing this pattern, I’ve taken a step I’ll bet MailChimp hopes doesn’t happen much.
I configured my mail server to sequester anything sent my MailChimp into a folder other than my inbox. It’s not going directly to spam, but it may as well be. I might survey the folder occasionally, but it’s out of my way. And the truth of it is that nothing of value is likely to come from MailChimp anyway.
This kind of thing wouldn’t be necessary if MailChimp was more serious about ensuring its clients were doing real opt-in. But they’re not, and I’m getting the idea that their whole business model is predicated on not being too much of a stickler on this point. They’re keeping out the Nigerian princes, but as far as I’m concerned the Marty McVey Mayoral campaign is no better than any other sort of unsolicited commercial message.
Take for example their “report abuse” method. First, you have to search their site to find a way to do this, but it’s there. Their approach involves a web form that requires the user know how to view the raw headers of the message to pull out a unique value that identifies the campaign and client.
Yeah, nobody is gonna do that. Nobody, I mean, other than me.
It’d be WAY simpler if there was always a “report abuse” link in the footer of every message sent through MailChimp, but that would produce actual reports of abuse, which are not in their interest. This way, they get to say there’s a mechanism for reporting and dealing with abuse, but their implementation means only nerds like me will ever bother doing so.
It’s reasonable to assume this means that MailChimp isn’t that interested in preventing abuse or getting reports of abuse from bulk mail recipients, because it’s bad for business. Most people who get spammed by a given campaign will just delete the mails when they come in.
As I suppose is obvious, at Amalgamated Heathen, we’re not most people.
The Soviets bugged typewriters in US Embassy from 1976 until 1984.
I sorta hope this crops up in The Americans.
Fancy a game of Loop? it’s played on an elliptical table. (via MeFi.)
(It’s got its own site as well.)
This article is completely brilliant. Read it.
I’m planning to upgrade my laptop this year, as is my custom. I do so every three years, give or take. Mrs Heathen usually takes my old one as hers for light duty (email, web, the odd Office doc), which also serves as my “emergency backup” machine until it’s recycled or donated when the next new machine enters three or so years later.
Laptops have gotten good enough that the three year cycle is starting to seem a LITTLE extravagant, but two things drive the upgrade this time:
There’s actually another factor, too: it seems like CPU power might finally have come to the point where I could buy something other than the top-of-the-line full-size Macbook Pro. Time was, a 4.4 pound laptop was svelte, but that’s just not the case anymore; the 13″ Retina Macbook Pro is a full pound lighter. (The Air and the newly introduced just-plain-Macbook are nonstarters for technical reasons.)
That said, I do worry a little: the 13″ laptop ships with a fast CPU, but it’s only a dual-core chip. The 15″ machines have quad-core chips, meaning they effectively have four CPUs while the smaller one has only two. And it’s not at all clear to me how much difference this makes to me.
I feel like my machine is only rarely CPU-bound despite its fairly heavy duty cycle — lots of Lightroom, plus I run a Windows VM all day every day. Memory is likely the bigger problem, plus I/O. But that’s a hunch, and I don’t want to marry a laptop on a hunch.
Turns out, there’s a tool I could use to watch my CPU usage over the course of the day. It’s an old-school command-line Linux-heritage tool called “sar,” but it comes with OS X. There’s lots of examples online of how to use it, but as is often the case with command line utilities, it looks like there’s some serious differences between the Mac version of sar and the Linux version.
No problem, right? Just ask Google, and be sure to specify the version of OSX!
Well, turns out, that doesn’t work so well.
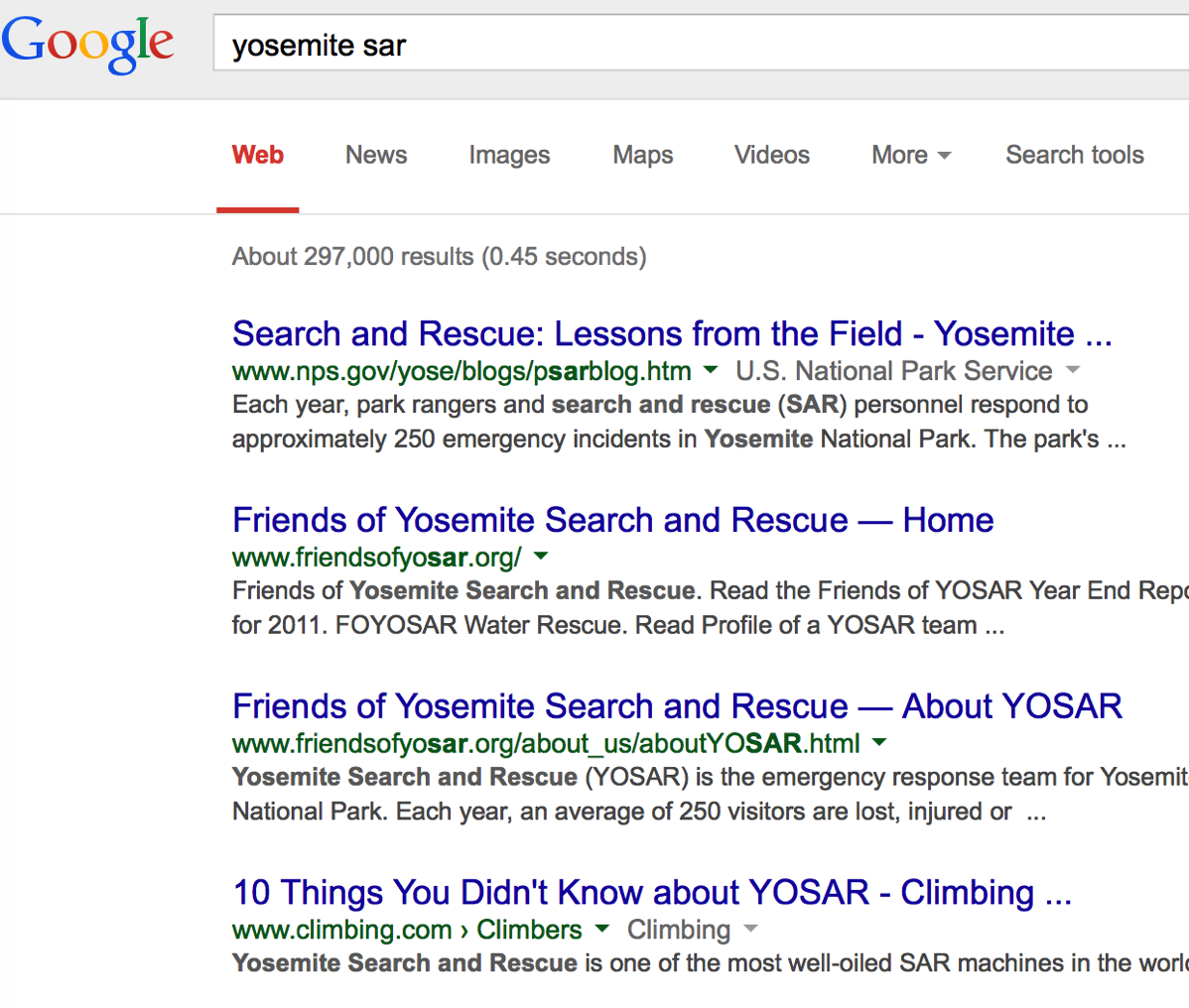
And if you understand why, you’re super, super nerdy:
If you use Chrome, you should try this.
If you don’t use Chrome, you should download it, and then try that link. It’s awesome.
I keep my personal calendar information separate from my corporate calendar. Work stuff is in an Exchange calendar, and personal stuff is in Apple’s iCloud calendar. Since the native Mac calendar can read from both servers, I can easily see my whole calendar there. Ditto on my iPhone and iPad.
However, heretofore, I haven’t bothered trying to show my iCloud calendars in Outlook 2010. It’s been a nagging thing-I-need-to-investigate for a while, but what pushed me over the edge was scheduling snafus brought about by the sudden influx of daytime medical appointments (scheduled, naturally, on my personal calendar) that were invisible to Outlook. See, 90% of the time, the calendar I consult before accepting a business appointment is the sidebar (“To-Do Bar”) calendar in Outlook.
That Outlook can’t see dinner parties is one thing. That it couldn’t see midday physical therapy sessions was becoming a problem. So, today, I went looking for a way to show all my cal data in Outlook, too. Turns out, getting that data in Outlook is pretty simple — you just download iCloud for Windows from Apple, and like magic you can see your contacts and calendars from iCloud in Outlook. Nice.
But because this is Microsoft, and they hate you, there’s a grotesque limitation. Sure, you can SEE your non-Exchange data in the Calendar mode in Outlook, but the To-Do Bar — which is the only calendar I ever use in Outlook — is limited to your DEFAULT calendar, and cannot show data from any other calendar, either from Exchange or another data source.
WAT.
This makes utterly ZERO sense, because even if I kept my personal calendar data in Exchange, it’d be in another calendar, not co-mingled with every business appointment ever. Having NO WAY to show a real and accurate sidebar calendar in Outlook is just baffling. Or, rather, it would be baffling, if it weren’t from MSFT.
So much for at-a-glance functionality. If I’ve gotta switch modes to see my days, I’ll just turn off calendars in Outlook entirely and use the Mac calendar instead, because this is some bullshit. It’s also bullshit that gets WORSE in Outlook 2013, since the To-Do Bar has apparently been significantly dumbed down there. More reason to eschew that particular upgrade.
Over at this Reddit thread, you can see a dress a woman made herself, from scratch.
By “from scratch” I do not mean a Simplicity pattern and fabric. I mean she started with a sheep, sheared it, combed the raw wool, then spun it into yarn, then wove the yarn into fabric, and then made the dress.
Oh, and she made the tools she used, too.
Some folks in New York have figured out how to 3-D print an actual dress. Not “print a bunch of pieces and then assemble them,” mind you, which is what I thought this would be when I first watched the video; I mean they created the design for this dress — comprised of thousands of triangles and other shapes linked together — that could be printed all at once, and worn immediately out of the printer.
This is seriously some William Gibson shit right here. Check it out.
JWZ details his work on a particularly excellent screen saver module; it draws pictures of “gear spheres” like this:

The math involved is, apparently, delightful.
Phil Noto will hit you right where you live. Seriously, make time.
The surest way to communicate to me that you know nothing is to mention the “[Brand X] Technology” included in the product in question, where “Brand X” is clearly a meaningless, made-up term, and then be unable to describe to me what that means, and then insist that “no, it’s not a made up term.”
You may also opt to compound your error by offering to show me Gartner “magic quadrant” graphs favorable to the product in question.
You may complete the trifecta by getting huffy when I poke you about the fundamental fecklessness of both points.
So, it turns out you can comment out comment characters in SQL.
-- /*
update resource
set IsDeleted=0, ExternalID=@externalID
where Code=@resCode
and ResourceSetID=@resSetID
-- */
Somehow, I made it 44 years without every really paying attention to the day to day differences in the time the sun sets. My agrarian ancestors would be horrified, I’m sure, but for most of my working life the only real question was “is it going to be light outside when I leave the office?”
In the summer, the answer is yes.
In the winter, the answer is no.
And for most of my life, that’s all I noticed.
But a couple months ago, I started riding with a group at West End on Tuesdays and Thursdays; the ride starts at 6:30, which is much earlier than the rides I’d done in the past. This summer has been great for my cycling; I’ve lost weight and gotten stronger, both of which have made me faster. The route to the ride doesn’t change, so I could gauge my progress by what time I pass certain points, and especially what time I get home.
The first thing I noticed was that my “great ride” finish time got closer and closer to 8:00; a couple times, I even got home BEFORE 8.
The second thing I noticed was that not only did I never turn on my headlight, but most of the riders I was with didn’t even bother to bring one. Sure, if you took breaks and didn’t plan to finish until the bottom half of the 8:00 hour, you’d need one, but if you mashed hard and kept moving you really didn’t need to bother at all in June (earliest sunset: 8:17, on the first), or in July (8:15, on the 31st)
Of course, after July 1, days start getting shorter again, and by mid-August I was using my headlight on the last parts of the ride even though I was finishing at the same time.
I started to wonder — never having bothered to care before — about the rate at which the day was getting shorter. I’d blithely assumed the change was linear at first, but there’s every reason for it not to be. It’s just that I never had cause to notice it before because I’d never been outside consistently during the time in question.
Being a giant nerd, I went looking for data. It wasn’t hard to find. This month the changes from Tuesday to Thursday, and especially from Thursday to the following Tuesday, have been especially pronounced; the table quantifies it, but in a way I didn’t anticipate.
The surprise was that yes, the acceleration IS there in the last half of the year — but it had already happened. Each day in September is about 1:45 shorter than the previous one; there’s almost no variance at all. The first was 1:44 shorter than the last day of August, and the 30th will be 1:46 shorter than the 29th.
The giant jumps happened two months ago. July first was only 22 seconds shorter than the last day of June, but by the end of the month the delta had ballooned to 1:17. The change in August wasn’t as huge, but it’s still much bigger than September: 1:19 on August 1 to 1:42 on the 31st.
I just didn’t NOTICE until September, because (a) the average day-to-day change in July is so much smaller and (b) if I’m honest, I admit that the need to use my headlight made me much more conscious of the rate of change.
But those big bites in September really do drive the point home. There’s only about a nine minute difference in daylight between July 1 and July 31, but those 1:45 changes add up quick in September. The 30th is more than half an hour shorter than the first.
My ride on the 11th had three and a half minutes less sunlight than my ride on the 9th, just two days before. My ride tonight will have nearly NINE minutes less sunlight than my ride Thursday.
tl;dr: Orbits and seasons, man.
I just needed to share a customer VPN landing page URL with a co-worker.
I have that link saved in my favorites bar, so I flipped over and did a right-click, chose copy, and then hit paste in the chat window.
And I got this:
/tmp/VMwareDnD/5141f9ae/New Client VPN.url
Whisky. Tango. Foxtrot. Under what fucking circumstances, Microsoft, would that EVER be something I wanted to share or copy? Any why would you decide NOT to have that action capture the underlying URL for the link?
I checked behavior in my other browsers; doing the right-click, copy thing with Safari and with Chrome yields the URL of the bookmark in question. Not so with Redmond, where apparently testing and polish remain utterly alien concepts.
XKCD suggests a universal converter.
This story about mistaken email identity reminds me of a tale from college.
Phone numbers on campus were, in dorms at least, more or less permanently set — room XXX would have phone number YYY, and it would stay that way. If you moved, your phone number changed. And if you knew that Dave lived in 213, you knew what is his phone number was — generally, one more that his neighbor to one side, and one less than his neighbor on the other.
This scheme was in place for years, and campus telecom liked it that way.
Well, they built a new rec center on the far site of campus, and the number allocated to the raquetball court reservation desk was a single digit off my friend M’s dorm room. He got LOTS of wrong numbers, often starting early on Saturday mornings. Campus telecom wouldn’t change either number despite his complaints, so he got creative.
He started accepting reservations, and giving out confirmation numbers.
It took about a week, but pretty soon the number for the raquetball courts changed. I can’t imagine how many irate players screaming about their confirmation number were involved, but 20+ years later it still makes me giggle.
For my whole career, I’ve been aware of babble and noise coming from “research” firms like Gartner and IDC. Their publications are, nearly always, bizarrely wrong or completely irrelevant to reality, designed mostly to please consultants who cite them and clueless CIOs who read them and feel clever, but neither pursuit has traditionally been tightly coupled to reality.
One of the drums they’ve adopted to beat loudly and often is the supposed decline of Apple, so much so that they declared Apple would suffer a DECREASE in Mac shipments this quarter — an announcement they made in advance of Apple’s own quarterly reports.
They were, of course, very very wrong, as Apple reported double-digit Mac sales growth in the period.
Apple’s sales figures not only contradict both IDC and Gartner figures, but also both firm’s market conclusions. IDC specifically reported that Apple’s Macs “lost market share over the past year. In U.S. shipments, Apple slipped to become the No. 4 PC maker, dropping from the No. 3 spot to come in at 10 percent market share, a 1.7 percent decline.”
IDC’s incorrect assessment of Apple’s double digit U.S. growth percentage as a year-over-year “decline” also calls into question its ranking of Apple as the fourth largest maker of conventional PCs in the domestic market, as the narrowest possible interpretation of Maestri’s “double digit” growth would essentially tie Apple with Lenovo in U.S. sales, according to IDC’s own figures.
More importantly, it also means Apple’s Mac sales continued to outpace the overall industry. Both firms reported that Apple lost share in the quarter. However, IDC estimated the U.S. PC sales increased by just 6.9 percent. Globally, it reported that PC sales fell by 2 percent in the quarter as Apple’s Mac sales grew by 18 percent.
Gartner estimated that U.S. PC sales grew at a slightly faster pace of 7.4 percent, still far behind the “strong double digit growth” Maestri reported for Macs. And Gartner’s numbers portray Apple and Lenovo as being even closer than IDC’s, suggesting that there’s no way Apple could have experienced a “double digit” percentage in growth without surpassing Lenovo to become the third largest vendor of conventional PCs in the U.S., behind HP and Dell.
Even more damning is the way they calculate PC vs. tablet sales:
In calculating their PC “market share” numbers, both IDC and Gartner include low end netbook and hybrid devices and Windows tablets. IDC also counts Chromebook web browser devices, but both firms exclude sales of Apple’s iPad from their PC sales figures.
If they had included iPads and other tablets in their PC figures, they would be forced to recognize Apple as being the largest computer maker by a wide margin. Despite much media handwringing about Apple’s year-over-year decrease in iPad sales, the company still sold 13.3 million iPads globally in the quarter, more than Samsung, Lenovo and Asus (the next three largest vendors, according to IDC) combined.
[…]
IDC, Gartner and Strategy Analytics have a long history of presenting carefully contrived data in press releases clearly designed to flatter their clients and denigrate their clients’ competitors, with Apple being a common target.
Beyond just serving the public relations needs of their clients, however, data promulgated by these marketing firms helped to obscure major shifts in the technology landscape, such as the clear and obvious shift away from conventional PCs that began with the appearance of iPad in 2010.
Fortune has an interesting backgrounder on how these estimates are created, and for whom, and (as you may surmise) reality doesn’t enter into it. Pleasing their clients does, and their clients are the other PC makers.
All of this is h/t Daring Fireball.
Tired of hearing about the Cloud? I’ve got just the thing.

As suggested by BoingBoing, let’s celebrate by watching Buzz Aldrin punch a moon-landing-denier in the face.
It has come to my attention that there exists a “no-code” website creation tool from Adobe called Muse.
Muse, like countless such tools before it, purports to allow a user to create and manage a site without writing any code. This is a laudable goal.
As with most such tools, the work is done locally, and the tool only sends the files to the web server when the user is satisfied they’re ready. The actual transmission of the files from the user’s machine to the web server is hidden.
Fifteen years ago, we could be pretty certain that the transmission was happening using FTP, a venerable protocol that has fallen COMPLETELY from favor because it’s staggeringly insecure. Nothing about it is encrypted — not even usernames and passwords. This means any fool with a sniffer can own your web site, which is generally considered a problem.
For this reason, FTP usage has dropped off considerably in recent years; I don’t think I’ve run a server with FTP enabled in over a decade. There is, however, a work-alike protocol that leverages the excellent SSH libraries to create a secure, encrypted transmission channel. It looks like FTP and acts like FTP, but under the hood it’s secure. This is a good thing. SFTP has almost completely replaced FTP as a result.
And this is why we know Adobe hates you, because Muse, a tool introduced in 2012, does not support anything but FTP, and they’re not planning to add SFTP any time soon. Their actual advice is to use an external FTP client if you need a secure channel.
Whiskey. Tango. Foxtrot.
Dear Adobe: DIAGF.
A long time ago, there was the boom. It was fun. It always is, with other people’s money. Then the boom stopped, and I needed work. I got a pretty good opportunity freelancing, and made a real living at it for a while, largely because I spent a good chunk of my suddenly “at liberty” time figuring out a new web technology called cascading style sheets, or CSS.
What they actually do isn’t important to the story, but I’ll note they were weird and different and confusing, and suggested major changes to the way web pages got built. That the change was a huge improvement, semantically speaking, didn’t make it easier for the folks mired in the old way. But I wasn’t, and so I waded into the deep end of CSS work unencumbered with “how we used to do it” -ism, and with a very serious weapon on my desk. A guy named Eric Meyer, see, had written a book called Cascading Style Sheets: The Definitive Guide (for O’Reilly, obviously), and I made it my bible.
With it, I managed not to go bankrupt. With it, I kept my house and my car and even had some money to spend on fun things. I was still leveraging these skills years later, in 2007, when I joined my current employer.
Because, in no small part, of that book, and of Meyer’s active participation in developer forums and the CSS-D listserve. And I’m certainly not the only person who has that kind of story about Meyer and his book and his activism.
I don’t do that sort of work anymore. I still find it fascinating, and I still read the blogs and now Twitter feeds of lots of the people who defined markup and web work in the early 2000s, which is how I found out that Eric Meyer’s young daughter had cancer, and how I found out, a little while ago, that she died on Saturday. She was six.
Six.
Today, apparently, is the day of the service. Web people all over are making their Twitter avatars purple, in honor of Becca Meyer, who had a favorite color as only children can. And this is where nerds make you cry.
In HTML and CSS, colors are typically specified by a six-digit code in hexadecimal, like #FF0000 (which is a red). You can, though, use just basic words for some colors. “Red” works, as does “blue” and “black” and even things like “lightcoral”.
There is an organized movement online now to include in CSS4 the named color “beccapurple”, equivalent to #663399, as a memorial.
I think that’s mighty fine.
This brilliant bit about beating Dragon’s Lair has been widely linked, but that makes it no less deserving of your time if you haven’t seen it.
This is one of those articles that’s so true it hurts. Here’s the first bit:
All programming teams are constructed by and of crazy people
Imagine joining an engineering team. You’re excited and full of ideas, probably just out of school and a world of clean, beautiful designs, awe-inspiring in their aesthetic unity of purpose, economy, and strength. You start by meeting Mary, project leader for a bridge in a major metropolitan area. Mary introduces you to Fred, after you get through the fifteen security checks installed by Dave because Dave had his sweater stolen off his desk once and Never Again. Fred only works with wood, so you ask why he’s involved because this bridge is supposed to allow rush-hour traffic full of cars full of mortal humans to cross a 200-foot drop over rapids. Don’t worry, says Mary, Fred’s going to handle the walkways. What walkways? Well Fred made a good case for walkways and they’re going to add to the bridge’s appeal. Of course, they’ll have to be built without railings, because there’s a strict no railings rule enforced by Phil, who’s not an engineer. Nobody’s sure what Phil does, but it’s definitely full of synergy and has to do with upper management, whom none of the engineers want to deal with so they just let Phil do what he wants. Sara, meanwhile, has found several hemorrhaging-edge paving techniques, and worked them all into the bridge design, so you’ll have to build around each one as the bridge progresses, since each one means different underlying support and safety concerns. Tom and Harry have been working together for years, but have an ongoing feud over whether to use metric or imperial measurements, and it’s become a case of “whoever got to that part of the design first.” This has been such a headache for the people actually screwing things together, they’ve given up and just forced, hammered, or welded their way through the day with whatever parts were handy. Also, the bridge was designed as a suspension bridge, but nobody actually knew how to build a suspension bridge, so they got halfway through it and then just added extra support columns to keep the thing standing, but they left the suspension cables because they’re still sort of holding up parts of the bridge. Nobody knows which parts, but everybody’s pretty sure they’re important parts. After the introductions are made, you are invited to come up with some new ideas, but you don’t have any because you’re a propulsion engineer and don’t know anything about bridges.
Would you drive across this bridge? No. If it somehow got built, everybody involved would be executed. Yet some version of this dynamic wrote every single program you have ever used, banking software, websites, and a ubiquitously used program that was supposed to protect information on the internet but didn’t.
Go read the whole thing.
(Via MeFi.)
BTW, Quinn Norton makes similar points here.
glasshole.sh. Heh.
Over on the Medieval Arts Resource Twitter, we find this bit of complete brilliance:
Start tracking their comings and goings without their concent by sniffing the Wifi ID on their smartphones and tablets, even if they don’t join your network.
Seriously, fuck shops that do this, and fuck Euclid Analytics for marketing the idea at all.
Tragically, these sounds may go extinct.
Also, if you turn on too many of them, your officemates may have strong feelings about your own survival. Exercise caution.
A three-word phrase that should trouble you: Accidentally Turing-Complete.
A Reuben’s tube is an apparatus used to demonstrate standing waves in physics; it’s akin to the gas lighter in your fireplace, but with sound added. At certain frequencies, the flames will vary according to the standing wave produced in the tube.
Things get exponentially more awesome if you make a 2-D tube, and apply more interesting music. At the link, the vid is cued to the music, but it’s really worth watching the whole thing.
So the net was aflame over Mozilla naming known homophobe Eich to CEO, and he was (rightly) out of the job just as quickly.
Having Condi Rice on the board of Dropbox is insanely worse. She’s objectively pro-torture, and represents the administration that put the NSA programs in motion — and now she has a position of authority at a company that holds users’ potentially private data?
Fuck a BUNCH of that. Might be time to DropDropbox.
I have been in this meeting a thousand thousand times.
In fact, it was a meeting like this one that prompted the conversation that birthed the NoGators.com domain name.
A Comcast exec issued a completely mendacious statement in response to Netflix CEO Reed Hasting’s rather frank and damning comments this week.
The folks at Consumerist have a fucking field day with it. Go read it.
Unless you have built your son his own “working” Mission Control panel, you are apparently not in the running.
Use an Apple device? And by this I mean any iPad, iPhone, or Mac?
Then you need to install all available OS updates with a furious quickness, for there is a security bug to end all security bugs in the SSL code on your device. All platforms are affected.
It’s a seriously bad, bad, bad bug. It may be the worse security bug of all time. No certificate validation is happening, which means that site you think you have an encrypted connection to might not be who they say they are. That’s an ID thief’s dream come true.
This bug is bad enough that it’s entirely possible that it was deliberately introduced at the behest of the NSA. The crypto we use daily relies on provably unbreakable encryption, so the only vulnerabilities they can exploit rely on broken implementations; this is a known tactic that the NSA and similar organizations have used. The timing certainly works.
More here.
You can check to see if you’re vulnerable using this site. On a Mac, you’ll need to use Safari to get the best possible reading, but it’ll mostly work with other browsers.
Shoring up the argument that it’s part of a deliberate effort: an even worse bug has subsequently been discovered in the Linux GnuTLS code.
Skipping the technical stuff, the takeway for you, the Heathen reader, is that you absolutely MUST upgrade your iOS devices and Macs today, right the fuck now. Full stop.
Fortunately, Apple makes this pretty easy. Just go to Settings -> General -> Software Update on an iPhone or iPad, or to (Black Apple) -> Software Update on a Mac.
My company routinely deals with government entities that have legitimate security concerns, so it’s not surprising that, sometimes, I receive mail that is digitally signed, or has some encryption component.
Usually, this is done poorly, which is no surprise, because mail encryption is still not seamless. However, yesterday I got a mail that Outlook won’t open at all. Instead, I get this:
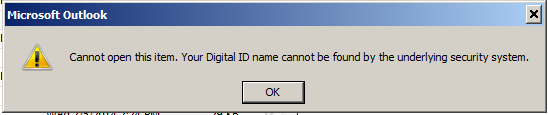
The hilarious part of this is that the mail opens fine with no hint of trouble when read from my Mac’s Mail.app client, or from either of my iOS mail clients. Security, Microsoft style!
Back in the boom, we tried to use online meeting tools, which inevitably led to shit-tons of time wasted at the head end of every meeting trying to get LiveMeeting to work.
It never really did.
In the years since, other companies have entered this space, and some of them are basically flawless. Trouble is, the good ones cost money, and most of our customer IT orgs are (a) cheap and (b) too paranoid to let their people use GoToMeeting, so we get forced into trying to connect with the execrable “Lync” — i.e., rebranding LiveMeeting bullshit — across the Internet.
MSFT makes their products so that they’re effectively free, but never bother solving for corner cases — like, say, a cross-site meeting that’s not all on the same network or active directory domain. Worse, Lync has no end of weird foibles and fuckups. For example, if you end up on 2013 instead of 2010 (which will happen if you upgrade Office), it’s no longer possible to join a meeting without having corporate credentials on the hosting party’s network.
That’s fine, though, because obviously nobody ever wants to meet with people outside their company, right?
CHRIST. It’s enough to make you want to strangle someone.